Internet Security Threats in 2017
2016 was a big year for new internet security threats coming to light. It may go down as the worst year to date for online privacy infringements and Distributed Denial of Service Attacks (DDoS) attacks. IT professionals have seen a large increase in attacks against business internet infrastructure, from desktop systems all the way to critical business servers. There has been a rash of internet security threats, the largest DDOS attacks on record, and ever-increasing government surveillance laws that make the internet a difficult landscape to traverse safely. Staying on top of new security threats is more important than ever, especially if you want to keep your critical applications and systems safe from becoming a headline on the evening news. What does 2017 have in store for us? Here is a look at the new internet security threats we could encounter during the New Year.
Over 1 Tbps DDoS Attacks
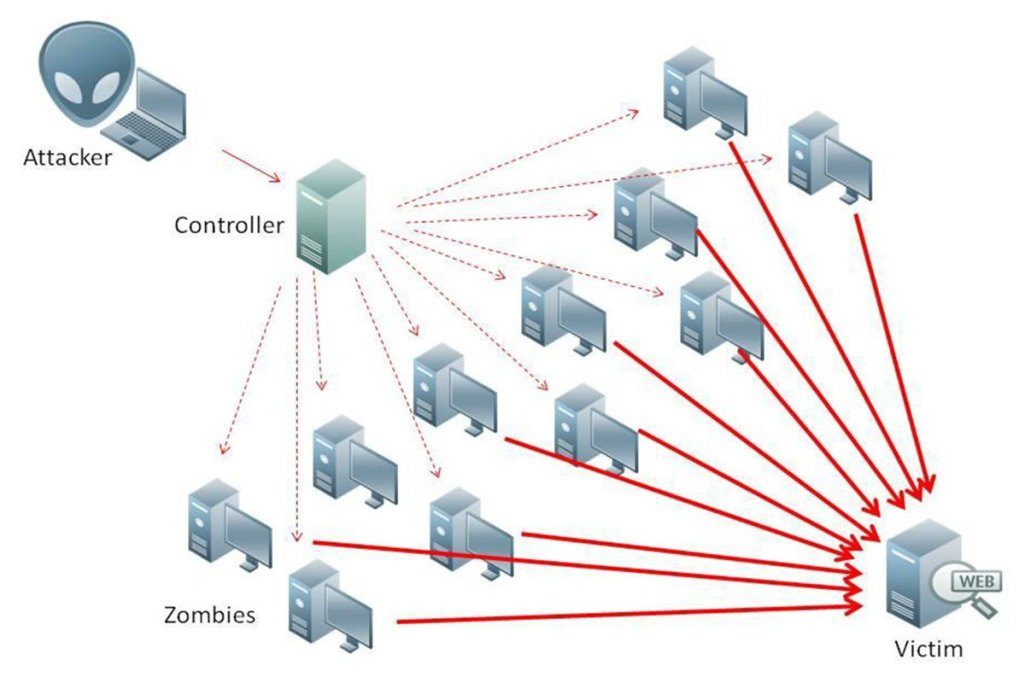
DDoS attacks rose to new heights in 2016, with attack speeds breaching marks of over 1 Tbps. This significantly increased attack speed was due in part to the hijacking on insecure Internet of Things (IoT) devices, allowing hackers to take down an entire hosting provider with minimal effort. DDoS has been one of the biggest problems in internet security to date. The rise of IoT based DDoS is only going to increase as more and more connected devices are added to the already massive pool of addresses on the known internet. In the past, hackers were creating botnets of desktop computers. Now they are able to take over smart device’s in the same way, creating zombie devices that can be bent to the will of the attacker. We are likely going to see more high profile attacks like this in the future—with even faster speeds—which means securing your IoT devices is paramount to protecting yourself and others.
Drone Jacking

Drones are taking the world by storm, but they aren’t secure and are a goldmine for disreputable activity. In 2016 the hobby and business sectors generated large amounts of income for this budding market. Logic points to new hacks and exploits being on the rise in 2017 to match the increase in drone usage across the country. Drones open up new types of internet security threats in this budding market. Research has found evidence that you can hack a drone and control it with minimal hardware and understanding of the technology. This has lead to a push for increased security standards for drone equipment. Companies such as Amazon and UPS have announced plans to delivers packages via drones to consumers, which means an enterprising hacker could hijack and intercept packages meant to be delivered to their consumers. Law enforcement agencies have been using drones for surveillance purposes and it’s expected that people are working on the ability to intercept video and audio feeds from drones for the purpose of disarming them or using them for more nefarious activity. Drone technology is still a relatively new industry and major security issues can arise if security recommendations are overlooked.
IoT Malware Surge

Iot malware was the new kid on the block and made waves in 2016. The high-profile DDoS attacks that ravaged hosting providers were able to take place due to unsecured IoT devices being infected with malware. As IoT devices become commonplace in the home, they will be under siege from hackers. Since many smart devices are simple, no frills systems sold as units that just work, people that buy them rarely will update or replace until long after purchase—as they are unaware of the danger they could pose. Many IoT devices are made with minimal features and security to help shorten the development costs and processing time. This is dangerous because it usually means easier backdoor access to the device. Once one device is compromised, it’s infinitely easy for an attacker to take control of whole interconnected system of devices. Smart devices may ship with a backdoor or malware installed by default in 2017 and it’s going to be a privacy concern we should not ignore.
Mobile Ransomware
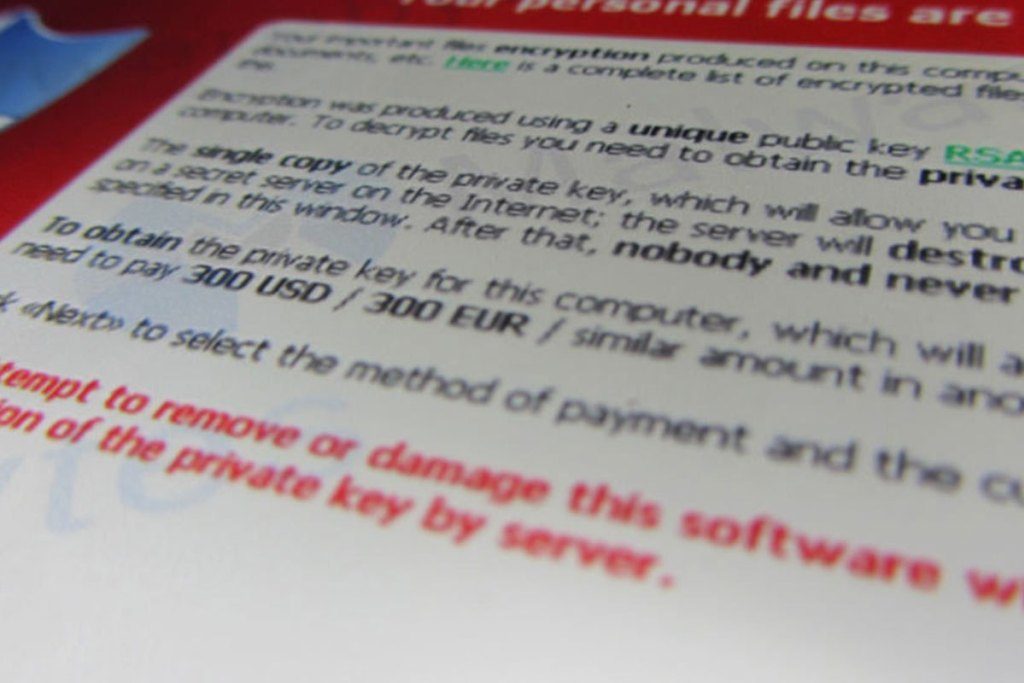
Ransomware has been on the rise in 2016, infecting and encrypting systems worldwide. Ransomware is malware program that is installed on a system that encrypts and then blocks access to your important system and user files. This block can only be removed with a decryption key provided by the creator of the malware. Victims are made to pay the ransom with anonymous bitcoins in order to regain access to their files. Most ransomware in 2016 found a home on desktop computers, but 2017 is projected to bring an uptick in mobile phone ransomware. With mobile variants popping up on android, law enforcement is cracking down on them and urging users to only download from trusted sources. Mobile ransomware is particularly scary since most people have their data backed up to the cloud and use their mobile devices to access more and more of their important personal data.
Government Surveillance/Censorship

Internet Freedom has been on the decline for years and there is no sign of it stopping or even slowing down. 2016 was an ugly year for internet liberty, as there were crackdowns on data retention laws, messaging apps were attacked, and social media bans were introduced. These attempts to limit privacy are a direct push towards mass surveillance. This is considered to be the greatest threat to privacy and security of them all. This past year we uncovered tons of information on how, where, when, and why governments used backdoors and other types of undisclosed information gathering techniques against their citizens. Unprecedented new surveillance laws have been passed in the US, UK, EU, which allow mass hacking and collect of data with absolutely no oversight. This is a disaster for business security, as many of the tools the government uses are unknown to the public.
Image Based Exploitation

Possibly the most scary internet security threat of 2016 came from the images we love so much. Images in 2016 have become a scary new entry point for exploitation of systems. Enterprising hackers have discovered a near bulletproof way to embed malicious code within an image that runs when the image is clicked. In the last quarter of 2016, advertising platforms were taken by storm as hackers used the technique to embed exploits in advertising campaign images. These were able to detect if a system was exploitable and run the package when the image was clicked. In seconds, the malicious code was run and the local system was compromised. This has been used to push trojans, backdoors, spyware, file stealers, and ransomware to internet users without their knowledge and there is no way to detect if they have been exploited. This affects all known web browsers and has no means of detection via virus software. This leaves 2017 wide open to a whole new undetectable exploitation system that potentially makes some of the internet’s most widely shared image formats a danger to everyone.
How to keep yourself secure in 2017
With all the interesting developments around internet security threats in 2016, it is critical to understand the best possible way to protect yourself or your business. That is to remain vigilant of your online activities. It is imperative that any internet user be careful of strange emailed links, unofficial download marketplaces, and suspect advertising images. Having strong passwords and being cautious of saving passwords within the browser or password keeper is paramount to keeping yourself secure. If privacy is important to you, having tools like a VPN and Proxy can ensure your data is being transferred securely, with encryption making it almost impossible to decode or track. With everything that happened in 2016, it does not look like privacy and security will fare better in 2017. Keeping your data secure is still possible, but big steps are going to need to be taken to get past the critical element of mass data collection initiatives. These initiatives pose data breach threats, as the centralized collection data looks much like a bank ripe for the robbing. All internet users need to keep their systems updated and use tools to ensure security and privacy while enjoying their online experience.
 Monty
Monty 

