COVID-19 has forced us to rely on technology in order to stay productive in our lives.
Since we’re now spending most of our time online, we should brush up on our privacy rights. There’s a need now more than ever to be aware of mistakes that will lead to getting our information hacked or companies stealing and selling your data.
The first thing you need to know about protecting your information is understanding the rights you have to it.
What are my rights?

There are ways to insure privacy protection but you have to know how to enforce it. Part of making sure that you are protecting your privacy rights includes knowing how to use the internet safely.
Cross-site trackers allow websites to track your online activity. A simple way to get rid of this feature is by turning on a ‘Do not track’ (DNT) setting in your browser’s settings.
Another way to protect yourself is by deleting your cookies.
Cookies are pieces of data about you that are stored on your computer. This can range from passwords to browsing history.
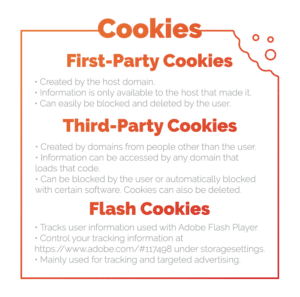
The best way to protect yourself here is by limiting your cookies.You can do this by deleting cookies in your settings or by finding a browser with limited cookie tracking.
Even though there are certain things you should block to gain privacy, there are other permissions you need to grant in order to use certain apps.
Some apps require your location, and that’s okay if you need Chipotle delivered to your door during self-quarantine. But some apps that ask for your location don’t need it to function.
Look out for apps that ask for certain permissions but might not need it.
Risky permissions may include:
- Location
- Audio-recording
- Camera
- Personal information
- Installing third-party apps
There are many other factors that contribute to what privacy rights you are giving away. Privacy is different with each device and there are certain ways you can project your data with each.
Your TV

In 2017, the CIA and UK’s M15 security was caught recording conversations from Samsung smart TV’s that appeared to be turned off.
The smart TVs were made to look like they are turned off, when really the TV is acting like a bug, recording and sending audio to CIA and UK servers.
This program was named “Weeping Angel,” and its purpose is to prevent us from terrorist attacks.
Who else receives information from my TV?
Smart TVs like Samsung, LG, Sony, Vizzio, and Roku record your viewing habits so that they could sell your viewing habits to manufacturers and other third-party companies.
Researchers at Northeastern University and Imperial College, London, found that almost all the TVs data was sent to Netflix, even if the app wasn’t installed and it hadn’t been activated yet.
Unfortunately, you can’t stop all your information from being sent out, but there are some things you can do in order to protect certain information.
What you can do:
There is good news and bad news.
The good: Although every TV is different, in most sets, you can turn off voice recording features and take extra steps that help protect your privacy.
Read through your TV’s privacy policies and user agreements to see what data is being collected and where it’s being sent to. It’s always smart to know who has your information and why.
You can also do your research before buying your smart TV.
Apple has pretty hefty privacy policies so their TVs don’t do much tracking. However, Chromecast and other Google TV products give the same data tracking information as when you sign up for other Google applications, like Gmail.
So when you find a smart TV you like, just be sure you’re comfortable giving away a certain amount of privacy.
If you’re looking for an in-depth article on how to turn data tracking off for specific smart TVs, check out this article from Wired.
The bad: Because apps collect your data anyways, there’s a reasonable amount of privacy you’re giving away to third-party sites.
For example, Netflix and Hulu will always record your data, whether you are streaming from a TV or not.
If you are wanting to escape tracking, it is important to know what data is being collected, where it’s going, and why they want it. This way, you know what information is being sent and why in some cases, you aren’t able to escape it.
Your Car

For 18 years, cops have had the technology to listen to audio from your car and retrieve your location in almost real-time.
This is called “Cartapping,” and happens when cops hand over warrants to vehicle tech-providers like OnStar and SiriusXM.
In one case, police retrieved data from OnStar from a Chevrolet Tahoe when the emergency button was accidentally pressed and an Onstar Staff worker heard people discussing a possible drug deal.
An officer followed the car while listening to the information, leading to the findings of illegal substances in the car.
Although the suspect had accidently pressed the button, the car was not signed onto OnStar’s service.
A GM spokesperson said that cartapping is something they don’t do unless they’ve been given a required court-order. This is because they want to make sure they’re providing a service while ensuring privacy, safety, and security.
In some court cases, lawyers have gotten the vehicle surveillance thrown out, because they argued it went against their reasonable expectation of privacy, guaranteed by the fourth amendment.
In other cases, cartapping was upheld because warrant’s were granted beforehand.
The answer to cartapping is simple: If you don’t want to be tapped, don’t give the police a reason to be suspicious of you.
Your Computer
According to tech retail company, Kensington, a laptop is stolen every 53 seconds. This means that in your lifetime, you have a 1 in 10 chance of it getting stolen.
When your laptop is stolen, the chances are high of getting your data hacked into.
Having a few security measures like remote-wiping and data encryption can help secure important information from being stolen.
Other ways to protect your privacy on your laptop include:
- Require a login password. Don’t make it easy for someone to hack into your computer. At the very least, have a login password.
- Use a Virtual Private Network (VPN). According to HowToGeek, “VPNs can be used to access region-restricted websites, shield your browsing activity from prying eyes on public Wi-Fi, and more.” So if you want internet browsing privacy with no data tracking, using a VPN is your best option.
- Make sure your software is always up-to-date. Software updates are often to fix bugs that can lead to hacking. It is always a good idea to update software as soon as it is available.
- Backup your data. If someone steals your computer, you don’t want to be at a loss when you can’t get any of your work or data back. Make sure you always have data backed up somewhere safe.
- Add a privacy screen and a webcam cover. Do you know how easy it is to install malware to hack webcams and laptop files? The malware is pretty easy to spot, but you can always add an extra precaution by having a webcam cover.
Do you think someone has hacked into your webcam? Remote-control malware allows a user to easily do this while also giving access to personal files, browsing history, and messages.
Luckily, all you have to do to solve this issue is locate the malware and delete it.
The process of deleting malware is different for every computer, but luckily Youtube or Google has the solution for just about every computer.
Virtual Assistants
In a world where virtual assistants are featured in almost every home, it’s crucial to know what information they are programmed to store.
Some companies, like Amazon, have built privacy programs that are created to make sure nobody can hack into your device. But what are they doing with your information?
Amazon made this youtube video to explain all the privacy protection features Alexa has, but never discusses what Amazon does with the information it receives.
Amazon doesn’t sell data that can be traced back to you but it does sell information on what you use Alexa for.
An example would be if you sent balloons to a friend on their birthday. Amazon could tell the third-party that someone ordered balloons or that 50,000 people have sent balloons through Alexa, but not specifically as to who.
Other companies that have similar products like Google’s Google home or Apple’s Siri have similar policies.
Some people also worry about being secretly recorded.
Smart devices start recording when you give them their wake up word (Alexa, what’s the weather today?) and stop after the interaction.
As of right now, there are rumors, but there is no proof that the CIA is listening in, like they were doing with smart TVs.
Your Cell Phone
Cell phone apps are selling your data so companies can store data on you.
Data includes call logs, email contacts, internet and calendar data, app information, and more.
Apps aren’t the only data collectors on your phone.
Some of the top communication companies in the country are notorious for taking data and selling it to third-parties.
The only real way around this is to do some research on your service provider and see if they’ve been caught selling data.
The FCC (Federal Communications Commission) wants AT&T, Sprint, T-Mobile, and Verizon to pay hundreds of millions of dollars in fines.
This is because telecom companies have been selling location data without the users knowledge or consent. They did this by sharing real-time location by pinging off nearby cell-towers.
Although they said they would stop, AT&T, Sprint, and T-Mobile were caught still doing it.
The notices are not final statements so the companies have the option to fight the fees.
Viktor Mayer-Schönberger, a professor of internet governance at the University of Oxford, explained the “sinister danger,” that these companies bring with storing our data.
The only way you can really avoid this is by using a pay-by-minute phone instead of investing into a plan.
Extra Steps to Reserve your Privacy

If all that isn’t enough for you, there are still extra things you can do to protect your privacy.
- Don’t post anything that you wouldn’t want anyone to use against you.
In other words, don’t post on Facebook that you go get coffee from Starbucks on Main st. every morning at 10:00am. You don’t want someone stalking you because you made it easy for them. - 2-Step authentication.
This makes it harder for your accounts to get hacked into. It is always a good idea to have this implemented. - Use different passwords.
This one is a no-brainer. If a hacker can figure out one password, then you are in trouble if all your passwords are the same. - Update, Update, Update!
It is common for apps or software to have updates that fix bugs. Update as soon as it is available to make sure you have the best available software. - Use browsers that are safe.
Browsers take all sorts of information and store it to sell to companies. Use protected browsers like Brave or Firefox for better privacy. - Use a Data Broker Opt-Out page
By using a reliable data broker opt-out page, you can delete your personal information from the largest databases. Some subscriptions even show what information was found and removed.
You’ve got your rights!

Even though there are some privacy aspects you do have to give up, there are many ways to protect yourself from getting spied on.
By knowing your rights to privacy, you’re better able to protect yourself from hacking and unwanted data sharing.
Want to learn more about privacy? Check out Fyresite’s blog and see how you can be efficient in internet security
 Lauren Lively
Lauren Lively 





